CIO Fireside Chat Recap: Responding to a Ransomware Attack

By Mario Brum, VP of Practice Area and Technical Advisory Services, GreenPages
Mario Brum hosted our inaugural CIO Fireside Chat, an online event for business executives and IT experts about the latest tech topics and trends. In this blog post, Mario recaps the discussion on responding to ransomware attacks and shares data from a real-time poll showing how top cybersecurity leaders responded to this controversial topic.
What should be the first thing an IT security leader does after a ransomware attack? It’s a question I asked during our recent CIO Fireside Chat online panel discussion. Imagine a CIO or CISO getting ready to leave on Friday evening for a well-deserved vacation who receives the bad news that ransomware is locking employees out of key data and systems. What next?
Jay Pasteris, the CIO and CISO of GreenPages, said the first thing that business executive should do is “consult his or her incident response plan.” In terms of cybersecurity, an incident response plan is a document describing how an organization responds to an event like a ransomware attack. “It’s your playbook,” said Pasteris, “that’s how you’re going to respond, how you’re going to get your team involved, and how you’ll communicate internally and externally. It’s a big advantage when you have one.”
Unfortunately, not every organization has an incident response playbook. Without it, businesses struggle with recovering from a ransomware attack. By developing an incident response playbook, your organization has a standardized plan to identify, remediate, and recover more quickly. “If you don’t have one it’s a scramble,” Pasteris explained. “Your reputation will take a hit if the news leaks to the press or you could suffer financially if data is leaked on the dark web. Every moment passing the situation just gets worse.”
Randy Becker, the Principal Security Architect responsible for offensive security and cloud security professional services at GreenPages, agrees with having an incident response playbook, but suggested including the organization’s legal department in that plan. “Ransomware attacks change a company,” said Randy. This is because emotions run high in the hours and days after an attack. Citing some real-world examples, Randy concluded that it never helps any organization to respond to ransomware attacks based on emotion. Bringing in a corporate attorney early on can help craft measured responses.
How Lawyers Can Help Plan Your Ransomware Response
GreenPages Cybersecurity Practice Lead Jay Martin pointed out that having corporate attorneys informed and engaged is good, but you don’t have to call your lawyer as the first step in response to ransomware. “There are things that can be done in parallel,” Martin said, noting that all businesses “should assume they’ve already been breached.” In his view, IT leaders should assume the breach happened before the ransom demand was published. This is because assuming a breach makes stakeholders more cautious when it comes to preparation and communications when a real event happens. As Jay explained, in a real emergency “the attackers could be sitting on your network and ‘listening’” as you’re formulating the response.
“For years, we thought about how to keep the bad actors out,” Pasteris mused. “But now we have to think they’re already in—and think about how we drive true business resilience.”
Understanding Risks to Business Resilience from Third Parties
What about when the vendors and partners external to your business are victims of ransomware? Randy Becker recounted how several major data breaches and ransomware attacks against large enterprises were caused by vulnerable third parties. So, if you’re a business-to-business (B2B) company with data and services consumed by other organizations, a ransomware attack “forces you to make a decision you never intended on making” said Becker, “because your customers rely on you.”
For example, your high tech B2B company has offsite backups available of ransomed customer data that may take eight hours or more to fully restore. However, if you have service level agreements (SLAs) guaranteeing customers access to their data in minutes or seconds, then your customers are down for a full business day while you restore. The point is that to achieve business resilience, CIOs and CISOs must think through all possible recovery scenarios when third-party vendors are involved. Performing a business impact analysis (BIA) against business services helps customers understand recovery requirements to reduce overspending when selecting vendors and SLAs.
Experts and Attendees’ Opinions on Paying After a Ransomware Attack
We’ve established that having a plan helps you to avoid paying a ransom, but what C-suite and Board members want to know is: Should we pay the ransom and move on from the incident? The short answer is “no.” All three GreenPages experts agreed that you shouldn’t pay because you’re dealing with criminals who are not honest and trustworthy people.
Jay Martin sympathized with those faced with the choice of either losing their data or losing their business, but pointed out you have no guarantee paying the ransom will get your data back. Randy Becker said the criminals often infect your returned data with malware that you can’t find easily and remove. Worst of all, Jay Pasteris noted that word will get around that you already paid once—then you risk your organization being hit over and over for a quick payout.
While some government entities make it illegal to pay the ransom, it is still big money for the criminals. Pasteris noted that if you compared the money stolen by ransomware gangs to every nation’s gross domestic product, ransomware is estimated to be “the third largest economy in the world. But it’s not like Deloitte is reporting on this because it’s illegal money.”
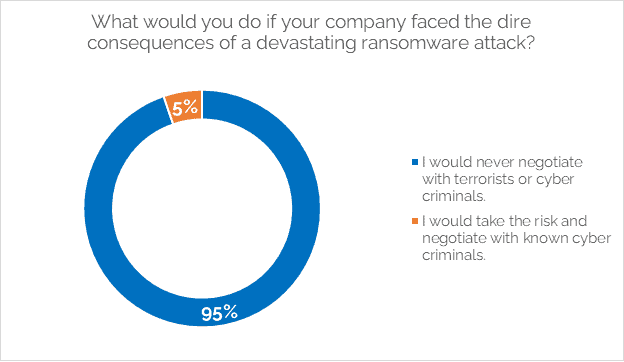
The overwhelming majority of live online attendees for the GreenPages CIO Fireside Chat agreed with the panel, as 95% of respondents voted to never negotiate with the ransomware attackers:
How to Build a Robust Incident Response Plan
When it comes to mitigating the impact of a ransomware attack, CIOs and CISOs agree their IT teams are in a race against time. GreenPages has a robust cybersecurity practice that will provide your organization with strategies built on proven frameworks that protect your cloud, network, and hybrid workforce environments from ransomware and other threats. Our cybersecurity experts consult with you to deliver a solution based on your business goals, risk tolerance, and budget.
Reach out to GreenPages to build a comprehensive cybersecurity solution today.





